ICT Security Tools and Techniques among Higher Education Institutions: A Critical Review | International Journal of Emerging Technologies in Learning (iJET)
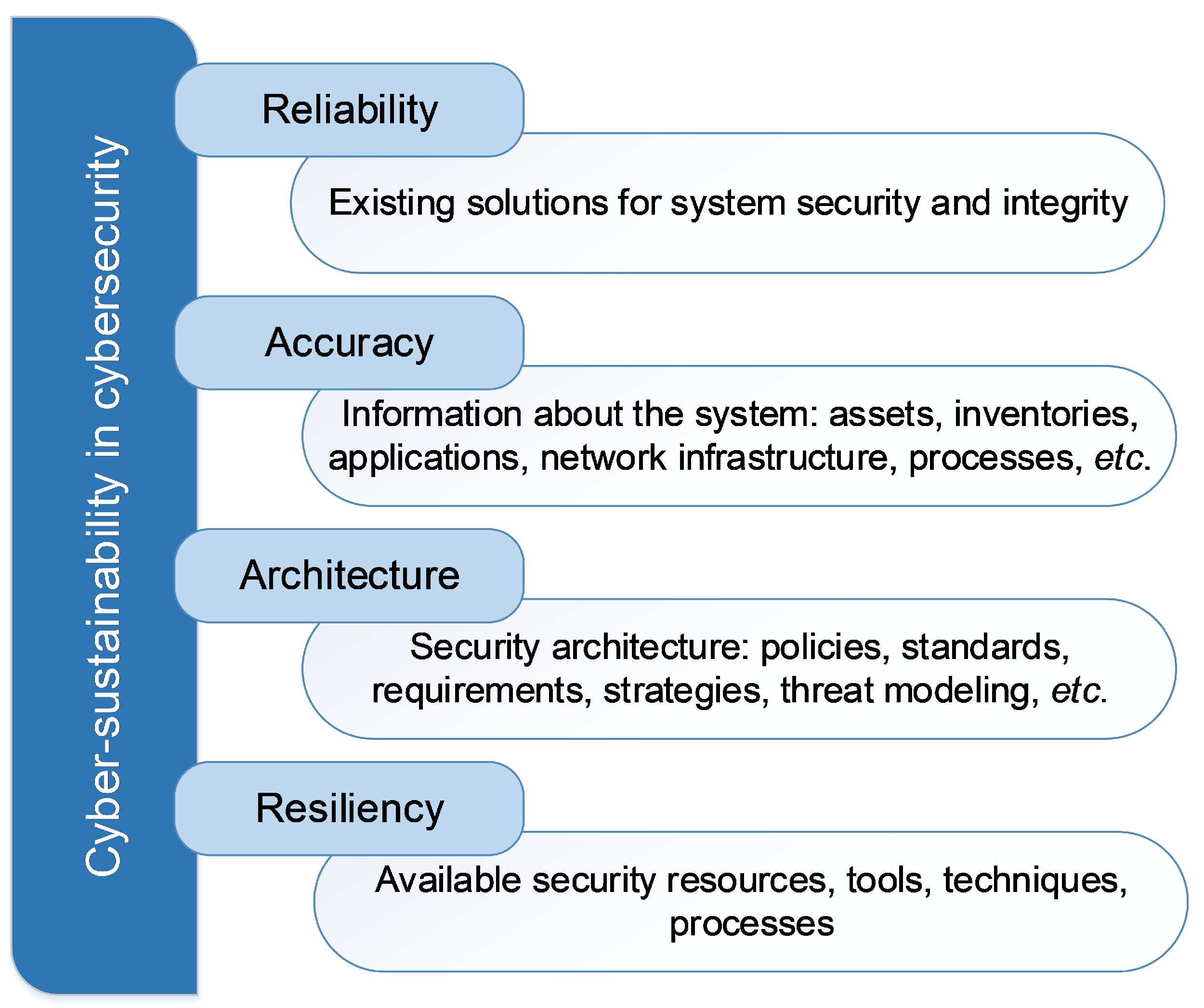
Electronics | Free Full-Text | The Method for Identifying the Scope of Cyberattack Stages in Relation to Their Impact on Cyber-Sustainability Control over a System








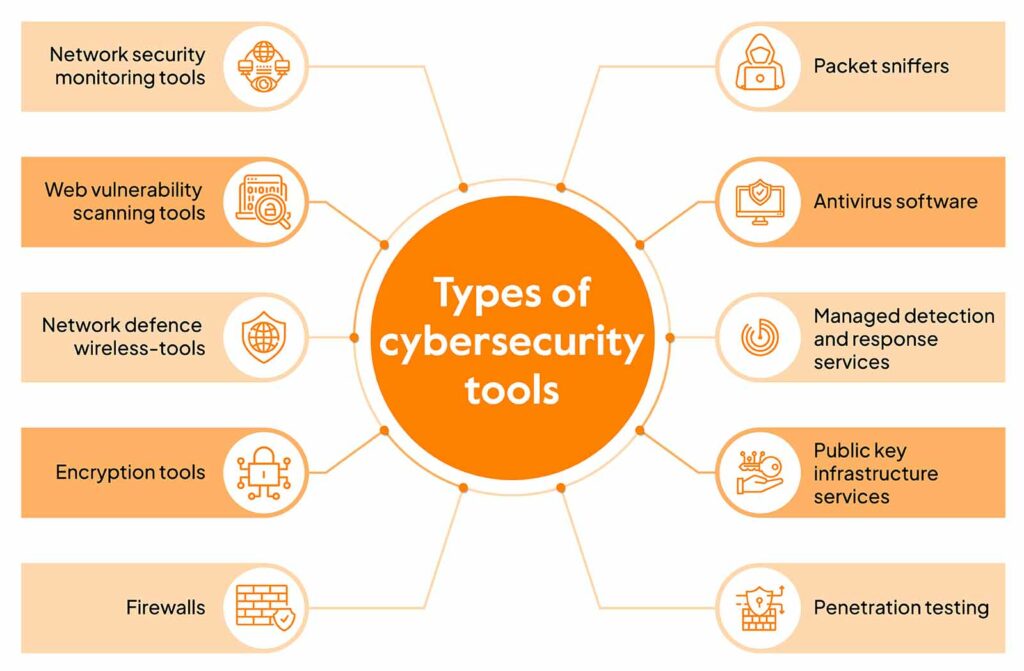
![Top 20+ Cyber Security Tools for 2023 [Paid+Free] Top 20+ Cyber Security Tools for 2023 [Paid+Free]](https://intellipaat.com/blog/wp-content/uploads/2021/06/Top-20-Cyber-Security-Tools-Big.png)